“How to Hack Facebook?” is one of the most searched questions on the Internet. Many of us badly want to hack into someone’s Facebook account but obviously that’s not an easy job, at least for a novice.
There are tons of websites on the Internet where you can find a variety of tools and methods on hacking Facebook but most of them are fake and the rest of them need technical expertise. Please beware of hacking tools, most of the tools actually hack your Facebook account instead of the target user.
If someone is able to hack Facebook account, it means they have an account takeover security vulnerability affecting FB. They can sell it to a black market illegally for millions of dollars. They can get instant fame and thousands of dollars in reward if they report the vulnerability legitimately through bug bounty program.
What do they get by sharing the method online, that too for free? What do they get for creating a free tool / software based on it? Absolutely NOTHING.
So the free hacking tools you see on the Internet are all fake. Don’t waste your precious time searching such hack tools.
If all the FB hacking methods need technical expertise, then how come a large number of people get their account hacked?
There are some methods like Phishing that can be easily done by using the resources available on the Internet. You can learn more about such Facebook hacking methods.
Also, see why Facebook rewarded me $10,000 USD for hacking Facebook mobile app’s private photos using a security vulnerability.
A thief might not always use your doorway to enter home. The same way, a hacker may not need your password at all the time to hack your Facebook account. Actually, most of the time a password is not necessary for a hacker to hack your Facebook account. Sounds weird? It would unless you are a hacker 😉
Hackers are not magicians to use tricks to get the show done. They do it in a hard way. They spend day and night researching to find a security vulnerability affecting Facebook. Hacking an account isn’t difficult once they have a vulnerability.
We are going to cover some Facebook hacking techniques discovered on bug bounty program that could have let anyone hack into any FB account WITHOUT PASSWORD. Please note that all the methods listed here are patched by the Facebook team and it no longer works. But you will get a basic idea of how hackers could hack an account without knowing the actual password. Check the link placed in each method if you want to view more details.
1. Hack any Facebook account with a mobile SMS
This vulnerability could allow a user to hack FB account easily in a fraction of seconds. All you need is an active mobile number. This flaw existed in confirm mobile number endpoint where users verify their mobile number.
Execution of this vulnerability is very simple. We should send a message in the following format.
FBOOK to 32665 (for the US)
You should receive a shortcode. Then, a request to the FB server with the target user ID, shortcode, and a few other parameters could do the magic.
Sample Request
Post /ajax/settings/mobile/confirm_phone.php
Host: www.facebook.com
profile_id=<target_user_id>&code=<short_code>&other_boring_parameters
That’s it. Sending this request to Facebook server with any user cookies can hack the target account. Your mobile number will be attached to the target user’s FB account once you get a response from the FB server. Now you can initiate a password reset request using the mobile number and hack into the target account easily.
This vulnerability was found by Jack in 2013. FB security team patched the issue pretty quickly and rewarded him $20,000 USD as a part of their bounty program.
2. Hack any Facebook account using Brute Force Attack
This brute force vulnerability leads to complete FB account takeover which was found by Anand in 2016. Facebook rewarded him $15,000 as a part of their bug bounty program.
This flaw found on reset password endpoint of Facebook. Whenever a user forgets his password, he/she can reset their password using this option by entering his/her phone number or email address.
A 6 digit code will be sent to the user to verify whether the request is made by the concerned person. The user can then reset their password by entering the 6 digit verification code.
One cannot try different combinations of the code more than 10 to 12 attempts since the FB server will block the account for password reset temporarily.
Anand found that mbasic.facebook.com and beta.facebook.com failed to perform the brute force validation thus allowing an attacker to try all the possibilities of the six-digit code.
Sample Request
Post /recover/as/code/
Host: mbasic.facebook.com
n=<6_digit_code>&other_boring_parameters
Trying all the possibilities (brute forcing) of the six-digit parameter (n=123456) allows an attacker to set a new password for any FB user. This can be achieved by any brute force tool available online.
Facebook fixed this vulnerability by placing limits on the number of attempts one can execute on the reset code endpoint.
3. Hacking any Facebook account using Brute Force Attack – 2
Arun found the same brute force vulnerability in another subdomain (lookaside.facebook.com) of Facebook that had got him $10,000 reward from Facebook in 2016.
Initially, they rejected the bug by saying that they are unable to reproduce it. The vulnerability was accepted only after a few weeks time and the patch was rolled out as soon as their security team was able to reproduce the issue.
And the sample request looks like this
Post /recover/as/code/
Host: lookaside.facebook.com
n=<6_digit_code>&other_boring_parameters
The attack scenario is exactly the same that we have seen in the previous method and the only difference is the domain name.
4. Hacking any Facebook account using a Cross Site Request Forgery Attack
This method requires the victim to visit a website link (in a browser where the victim should be logged into Facebook) to complete the hacking attack.
For those of you who don’t know about CSRF attacks, read about it here.
The flaw existed in claiming email address endpoint of Facebook. When a user claims an email address, there was no server-side validation performed of which user is making the request thus it allows an email to be claimed on any FB account.
You need to get the email claim URL before create a CSRF attack page. For that, try to change your email address to an email address that is already used for a FB account. Then you will be asked to claim the email if that belongs to you.
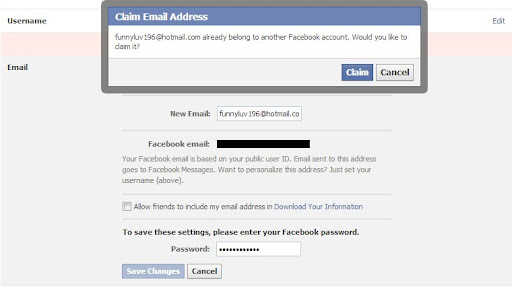
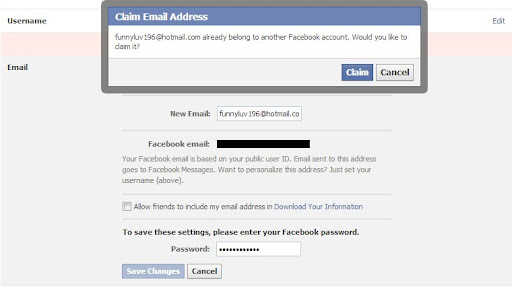
A popup with claim button should redirect you to the URL we need once we click on the claim button.
URL should look like
https://www.facebook.com/support/openid/accept_hotmail.php?appdata=%7B%22fbid%22%3A%22&code=<code>
You have got the URL. The last thing we have to do is to create a page to put the URL in an iframe and send it to the victim.
The email address will be attached to the victim’s Facebook account once he/she navigates to the URL. That’s it. You can now hack victim’s Facebook account through reset password option.
This CSRF account takeover vulnerability was found by Dan Melamed in 2013 and was patched immediately by FB security team.
5. Hack any Facebook account using CSRF – 2
This hacking technique is similar to the previous one where the victim needs to visit the attacker website for the attack to work.
This vulnerability was found in contact importer endpoint. When a user approves Facebook to access Microsoft Outlook’s contact book, a request to FB server is made that in turn adds the email to the respective Facebook account.
One can do this by Find contacts option in the attacker Facebook account. Then you should find the following request made to FB server (use intercepting proxy like burp)
https://m.facebook.com/contact-importer/login?auth_token=
The same GET request can be used to perfrom the CSRF attack. All you have to do is to embed the URL in an iframe in the attack page and share the link with the victim.
Victim’s account can be hacked as soon as the victim visits the attack page.
This bug was found by Josip on 2013 and patched by FB security team.
6. Hacking any actions on Facebook account – A CSRF Bypass
This CSRF vulnerability allows the attacker to take over the account completely and also it has the ability to perform any actions like liking page, posting a photo, etc. on the victim’s Facebook account anonymously without hacking into the account.
This flaw existed in the ads manager endpoint. The sample account take over CSRF request look like this
POST /ads/manage/home/?show_dialog_uri=/settings/email/add/submit/?new_email=<attacker_email>
All the attacker has to do is to craft a CSRF page with a form to auto submit the post request in an iframe when the victim lands on the page. The attacker’s email will be added to the victim’s account anonymously.
Then the attacker can hack into victim’s Facebook account by resetting the password.
This was found by Pouya Darabai in 2015 and got a bounty of $15,000 through Facebook bug bounty program.
7. Hack any Facebook page without being an admin
This Facebook page hacking method was found by Arun in 2016 and has got a reward of $16,000 USD for it.
Business manager endpoint used to assign a partner was vulnerable in this case. Changing the partner business asset ID parameter to a page ID allowed Arun to hack into any page.
Sample Request
POST /business_share/asset_to_agency/
Host: business.facebook.com
parent_business_id=<business_id>&agency_id=<business_id>&asset_id=<target_page_id>
Business ID parameter should be assigned to the attacker’s business ID and asset ID parameter should be replaced with the target Facebook page ID.
That is it. Now the target page should be owned by the business. The attacker can remove the existing page admins to completely take over the Facebook page.
8. Hacking Facebook user’s Private Photos
This private photos vulnerability was found by me in 2015 and got a reward of $10,000 as a part of their bounty program.
What do I mean by Private photos in the first place? The photos that you have in mobile and not published to Facebook those are the ones I mean when I say private photos.
The mobile app has a default feature called syncing mobile photos. Interestingly this feature was turned on by default in some mobile phones.
This feature uploads your mobile photos to FB server but keeps it private until you manually publish it to Facebook.
A Vulnerability in an endpoint handling these private photos allows any third party app to view/access user’s private photos. For this attack to work, the third party app must have access to user’s public photos, only then it can access the private photos.
Sample request to Graph API to access the private photos of victim looks like this
GET /me/vaultimages
Host: graph.facebook.com
access_token=<victim_access_token>
That’s it. The response from the API endpoint should have the URLs to private photos of the victim.
Facebook patched the issue by whitelisting the apps that can access vaultimages endpoint.
9. Hacking any Facebook user’s Photos
Arul Kumar found a way to delete any photo on Facebook in 2013 and they rewarded him $12,500 for his efforts.
Facebook has a feature to report photo to the owner if someone want to get the photo removed. The owner of the photo gets a notification and a link to delete the photo once reported by someone.
Arul found that the support dashboard photo reporting feature wasn’t validating the owner IDs properly thus it allowed him to replace the owner ID parameter with his own Facebook account ID to get the photo deletion link directly.
Then the attacker can delete the photo with the help of gained link from the exploit. The worst part about this attack is that the victim won’t know the photo was deleted. This vulnerability is completely fixed now.
10. Hack any Facebook user’s photo/video Albums
This vulnerability was found by me in 2015 that allowed me to take down any albums on Facebook. Albums with thousands of photos and videos can be deleted instantly without the interaction of its owner.
Graph API is the primary way of communication between the server and native/third party apps. Albums node of Graph API endpoint was vulnerable to insecure object reference thus it allowed me to issue any user’s album ID to process the deletion.
A sample request to delete any Facebook photo album
POST /<album_id>
Host: www.facebook.com
access_token=<top_level_facebook_access_token>&method=delete
This could delete the album specified in the ID parameter. The attacker should have the permission to view the album to complete the attack. Facebook patched this issue by fixing the endpoint to only allow users with privileges and rewarded me $12,500 USD for reporting the vulnerability.
11. Hack any Facebook videos
Pranav found a vulnerability that allowed him to delete any Facebook videos without concent permissions.
Facebook has an option to add video to comments on any post. Pranav found that attaching existing videos to a comment is possible and deleting the comment could let us delete the source video easily.
So the attacker should try to edit an existing comment on a post with the someone’s Facebook video ID through the following graph API request.
POST /<post_id>/comments?attachment_id=<target_video_id>
Host: graph.facebook.com
The target video should be added to the comment. Now the attacker has to delete the comment to delete the source video. The video should be deleted in few seconds as soon as the comment is deleted.
